
Executive Summary
Consolidated case for anonymized client (dur***), with full-scope WordPress incident response: immediate containment, technical forensics, malware eradication, operational recovery, and post-incident hardening.
Technical lead: Percio Andrade Castelo Branco (Infrastructure and Cyber Defense).
Technical Scope Delivered
- Incident response with isolation of the compromised environment.
- Application-layer forensics (WordPress), files, and database.
- Eradication of backdoors, malicious plugins, and unauthorized admin accounts.
- Remediation of the intrusion vector and review of vulnerable components.
- Hardening of credentials, permissions, and attack surface.
Context and Severity
The environment was received in critical condition, with full operational compromise of the site and active malicious actor presence. We observed privilege abuse, content tampering, creation of unauthorized administrative users, and monetization/extortion attempts. The client domain was anonymized and all sensitive indicators were sanitized.
Extortion Message and Threat Actor Attribution
During the forensic collection phase, we identified an extortion message attributed to the threat actor, originating from hacker@bwmakassarbeach.com. The message claimed database exfiltration, threatened public disclosure, and demanded payment in cryptocurrency.
- Observed channel: extortion email linked to the incident.
- Demanded amount: US$ 3,000 (message reference: 0.10 BTC).
- Wallet provided:
37J6b5DADjC5WubZX5PCGNTg2WXjdVa3Fa. - Coercion window: 72 hours after the message is read.
From a threat intelligence standpoint, the text only mentioned a "hacking group," without a reliable signature of a named group (no verifiable claim of a specific cartel/ransom crew). Therefore, attribution in this case remained at an unnamed actor level, focused on TTPs and technical eradication rather than brand speculation.
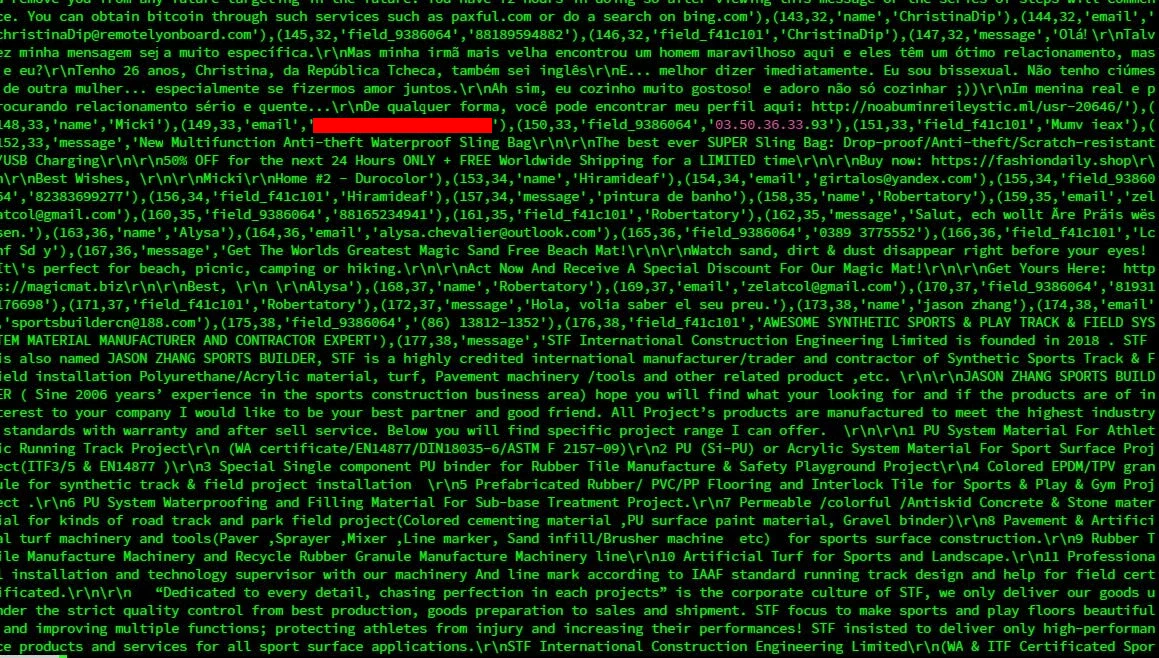
Preserved textual evidence (full excerpt)
"We have hacked your website duro*** and extracted your databases. This was due to the security holes you had in your your site/server which have gained us remote control of everything that was on the server.
Our team is mostly interested in customer, administrative, and employee information which we have extracted through your databases once we got remote control over the server. It still needs to be sorted out but it will be well-organized once finished. First, we will be going through the emails/sms information and contacting the recipient how you held in disregard about their information being exposed to a hacking group when you could have stopped it. This would be detrimental to your personal image with these relationships with these people. Lastly, now that we have information not only will we be monetizing off it with our methods but made public or sold to other people that will do whatever they wish with the information also after we are done.
Now you can put a stop to this by paying a $3000 fee (0.10 BTC) in bitcoin to the address 37J6b5DADjC5WubZX5PCGNTg2WXjdVa3Fa We will be notified of payment which we will then delete the information we have obtained, patch the hole in the site/server which we got in and remove you from any future targeting in the future. You have 72 hours in doing so after viewing this message or the series of steps will commence. You can obtain bitcoin through such services such as paxful.com or do a search on bing.com"Professional stance adopted: no negotiation with the threat actor. The response focused on containment, evidence preservation, eradication, hardening, and post-incident validation.
Shareable Technical Incident Data
Based on the forensic documentation (DURO***_SECURITY-3.0), the following data is shareable in a professional technical context:
- Operational severity: classified as 10/10 at incident activation.
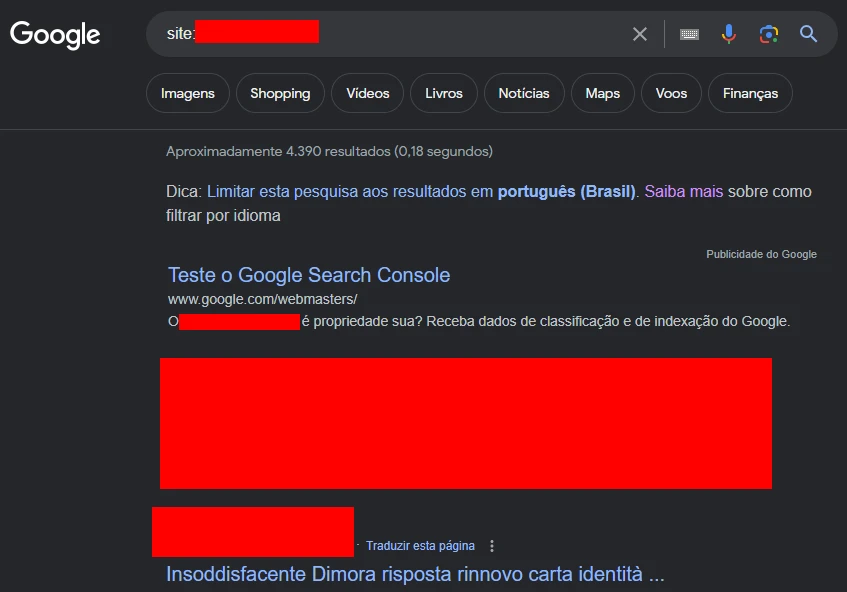
- Impact scope: WordPress application compromise (site), with no evidence of structural DNS domain compromise.
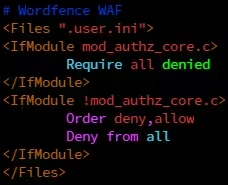
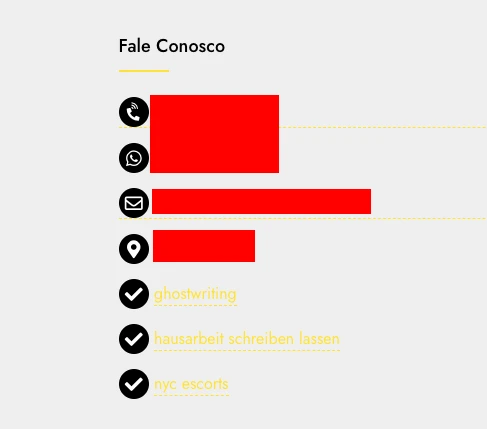
- Content abuse volume: 632 malicious posts published under the site account.
- Unauthorized admin accounts identified:
happy,wp_update-tSOhYl9s,wwwadmin,zadminz. - Primary confirmed vector:
Smart-Custom-Fieldplugin with webshell in file/wp-content/plugins/smart-custom-fields/classes/fields/class.field-class.php. - Artifacts detected in advanced scanning: 1,258 files flagged during the sanitation cycle.
Observed malicious infrastructure (sample)
Attacker automation patterns were observed across multiple plugins and temporary persistence directories. Sample artifacts listed in the dossier:
/wp-content/plugins/Cache/*
/wp-content/plugins/Hello_Dolly/*
/wp-content/plugins/kzwfkzk/*
/wp-content/plugins/nhoerxl/*
/wp-content/plugins/ofjubmt/*
/wp-content/plugins/t_file_wp/*
/cgi-bin/6573e397d142b/*
/wp-admin/images/resize-8x.png
/wp-content/cache/min/.ba4b87b5.ccssTactical Mapping (MITRE ATT&CK - Operational Reference)
- T1190 - Exploit Public-Facing Application: exploitation of a vulnerable WordPress component.
- T1505.003 - Web Shell: presence of an embedded webshell in a plugin and malicious PHP artifacts.
- T1136 - Create Account: creation of unauthorized administrative users.
- T1565 - Data Manipulation: mass content/post manipulation to distribute a malicious campaign.
- T1499/T1491 (efeito operacional): application integrity degradation and reputational impact.
Response Governance and Decision Criteria
- Non-payment decision: technical handling with no negotiation with the extortion actor.
- Initial priority: contain live attacker access and preserve evidence for structured analysis.
- Recovery criterion: return only after clean scan, privileged account review, and hardening completion.
- Incident exit criterion: consolidated documentation for audit, technical history, and operational continuity.
Technical Evidence Identified

IOC evidence in compromised file/plugin.
1. WordPress persistence
- Creation of multiple administrative users outside normal operations.
- Automated mass publication of unauthorized content (hundreds of posts).
- Modification of files in critical directories under
/wp-admin,/wp-includese/wp-content.
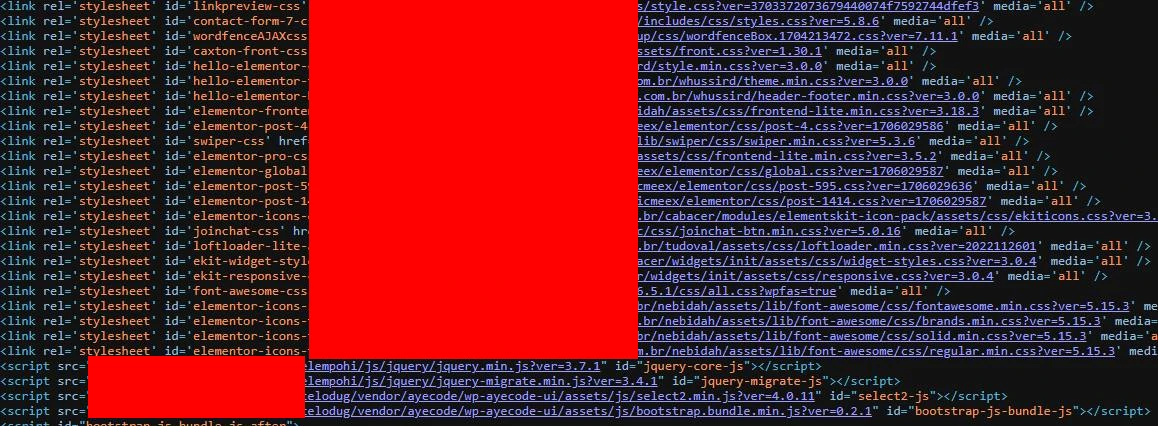
2. Malicious artifacts in files and plugins
- Presence of obfuscated PHP scripts and webshells in plugins, themes, and auxiliary directories.
- Injections in randomly named files to evade simple signature-based detection.
- Directory structure manipulation to maintain re-entry (backdoor persistence).
3. Compromise vector
A vulnerable WordPress component with embedded malicious code was identified in file:
/wp-content/plugins/smart-custom-fields/classes/fields/class.field-class.phpExploitation of this point enabled remote execution and escalation to administrative CMS control.
Technical capture of exploited vector in vulnerable plugin.
Applied Operational Methodology
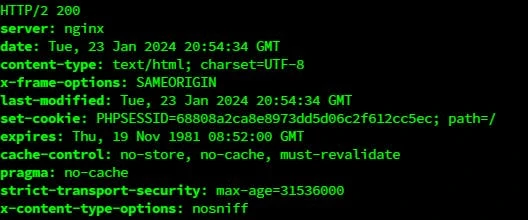
Phase A - Containment
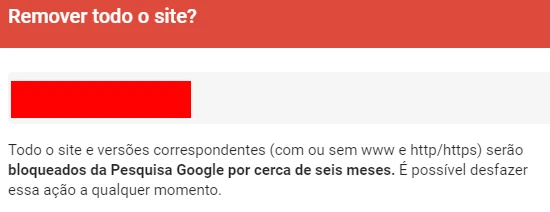
- Site removal from the originally compromised environment.
- Migration to an isolated environment to stop real-time attacker interaction during remediation.
- Evidence preservation for technical analysis before destructive cleanup.
Environment isolation and containment flow.
Phase B - Forensics
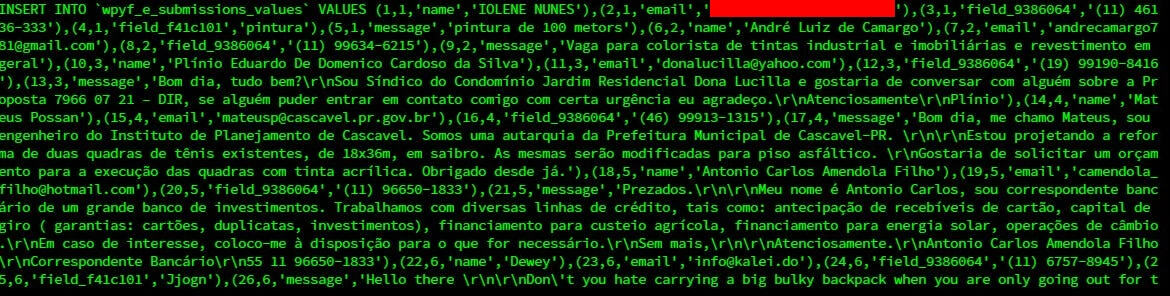
- Database analysis (content, users, abuse traces).
- Server and application log analysis (WordPress) for event timeline correlation.
- Combined IOC detection using multiple approaches:
- Known signatures (including hash/suspicious patterns).
- Heuristics for obfuscated patterns and anomalous behavior.
- Auxiliary Shell/Python routines for triage and inventory.
- Wordfence scanning in basic and advanced modes.
Phase C - Eradication
- Removal of malicious plugins and artifacts deployed by the attacker.
- Bulk cleanup of infected files and manual false-positive review.
- Removal of unauthorized administrative users.
- Sanitization of unauthorized injected content and records.
Eradication evidence (cleanup of files/unauthorized users).
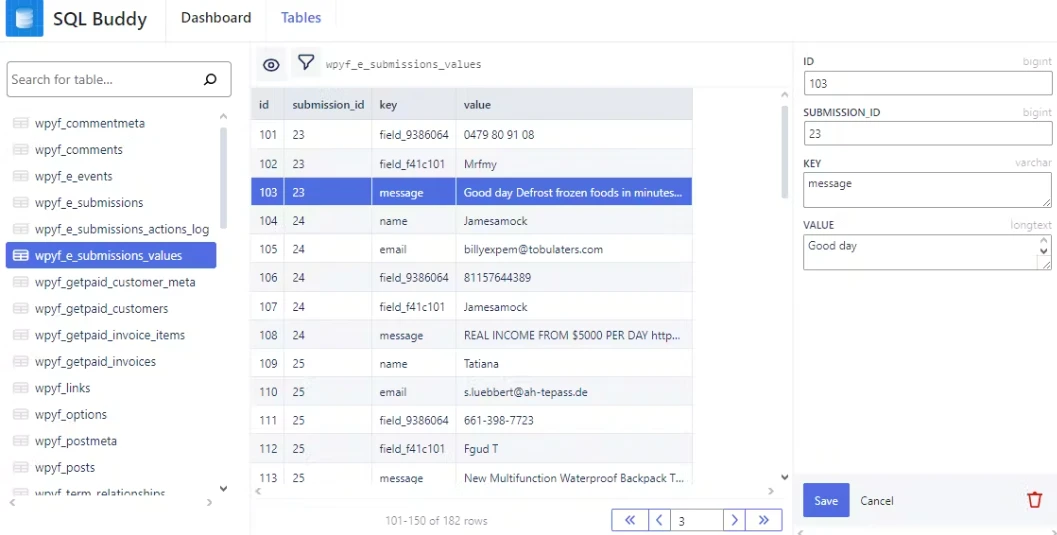
Phase D - Hardening
- Credential strengthening and administrative access policy enforcement.
- Plugin review and attack surface reduction (least-privilege principle).
- Application of WAF protection layer and additional WordPress security controls.
- Adjustments to reduce recurrence and improve continuous monitoring.
Final hardening state and active controls.
Examples of Indicators of Compromise (IOC)
During the engagement, IOC patterns were identified across multiple paths, including:
/wp-admin/images/*.png (unauthorized artifacts)
/wp-includes/blocks/*/*.php (malicious insertions)
/wp-content/plugins/*/*.php.suspected
/cgi-bin/*/wp-*.php
/wp-content/cache/min/*.ccssAdditional malicious automation trails were detected for directory and randomly named file creation.
Operational Metrics and Outcome
- Environment recovered from critical state to stable operation.
- A large set of malicious artifacts was removed (including samples in plugins, themes, and core).
- Unauthorized admin accounts removed and access control restored.
- Primary exploitation vector remediated and stack hardened to reduce recurrence.
- Technical documentation consolidated for audit, continuity, and security history.
Operational Timeline (T0/T1/T2...)
- T0 - Activation: incident received with evidence of active compromise and content integrity loss.
- T1 - Containment: removal from the compromised environment, isolation in alternate infrastructure, and live intervention blocking.
- T2 - Forensic Collection: IOC inventory across files, plugins, themes, and admin users; correlation with server and application logs.
- T3 - Eradication: artifact removal, cleanup of affected components, and elimination of unauthorized admin accounts.
- T4 - Vector Remediation: remediation of the vulnerable component and review of the extension/plugin identified as entry point.
- T5 - Hardening: credential reinforcement, attack surface review, access control, and WordPress protection adjustments.
- T6 - Validation: new scan round, functional test, and clean baseline confirmation.
- T7 - Delivery: final technical documentation, operational recommendations, and post-incident continuity plan.
Operational Timeline (UTC - Evidence)
- 2025-06-17 13:10 UTC: activation with evidence of active compromise and partial unavailability of legitimate content.
- 2025-06-17 13:20 UTC: compromised environment isolation and blocking of concurrent actor intervention.
- 2025-06-17 14:05 UTC: forensic collection started (IOC inventory in files, plugins, and users).
- 2025-06-17 15:30 UTC: primary vector confirmed in Smart-Custom-Field plugin (webshell).
- 2025-06-17 17:15 UTC: batch eradication of artifacts and removal of unauthorized admin accounts.
- 2025-06-17 19:40 UTC: hardening applied (credentials, permissions, attack surface review).
- 2025-06-17 21:10 UTC: post-remediation validation and controlled return to operations.
Operational Metrics (SOC/IR)
- MTTD (detection): low at activation (incident detected when already visibly active).
- MTTC (containment): ~10 minutes between activation and technical isolation of the environment.
- MTTR (initial technical recovery): ~8 hours for stable return with clean baseline.
- Cleanup scope: 1,258 flagged artifacts triaged/remediated in the full cycle.
- Content impact: 632 malicious posts removed/sanitized.
Stack and Commands Used (Real Operation)
Execution combined manual analysis, automation, and security tooling in a Linux + WordPress environment. Below are representative examples from the technical workflow applied:
Technical Stack
- System: Linux (Shell, POSIX utilities, grep/sed/awk/find).
- Application: WordPress (files, plugins, users, and content).
- Forensics and security: Wordfence, heuristic scanning, and signature/IOC analysis.
- Database: inspection and logical sanitization of malicious records.
Operational Commands by Phase
Phase 1 - Containment
# Initial logical snapshot (quick inventory)
find /var/www/site -type f | wc -l
find /var/www/site -type f -name "*.php" -mtime -14 | sort
# Direct search for common webshell/obfuscation patterns
grep -RniE "base64_decode|gzinflate|eval\\(|assert\\(|preg_replace\\(.*/e" /var/www/site
# Preliminary mapping of critical points
find /var/www/site/wp-admin /var/www/site/wp-includes /var/www/site/wp-content -type f \
| grep -Ei "themes\\.php|admin\\.php|index\\.php\\.suspected|\\.htaccess"Phase 2 - Forensics
# Administrative user triage (WordPress)
wp user list --role=administrator --path=/var/www/site
# IOC search in plugins and themes focused on the vector
grep -Rni "smart-custom-fields" /var/www/site/wp-content/plugins
grep -RniE "class\\.field-class\\.php|webshell|backdoor" /var/www/site/wp-content
# Syntax check on modified PHP (corruption detection)
find /var/www/site -type f -name "*.php" -exec php -l {} \\; | grep -v "No syntax errors"Phase 3 - Eradication and Hardening
# Post-cleanup permissions and ownership correction
find /var/www/site -type d -exec chmod 755 {} \\;
find /var/www/site -type f -exec chmod 644 {} \\;
chown -R www-data:www-data /var/www/site
# Operational cache cleanup and reindexing
wp cache flush --path=/var/www/site
# Final admin review after sanitation
wp user list --role=administrator --path=/var/www/sitePhase 4 - Final Validation
# Post-remediation rescan
grep -RniE "base64_decode|gzinflate|eval\\(|assert\\(" /var/www/site/wp-content
# Quick check of modified sensitive files
find /var/www/site -type f \\( -name "*.php" -o -name ".htaccess" \\) -mtime -3 | sort
# Basic functional check
wp core is-installed --path=/var/www/site
wp plugin list --path=/var/www/sitePost-remediation Validation
- Full rescan to confirm absence of active artifacts.
- Administrative authentication test and high-privilege account review.
- Functional validation of home and critical pages after fixes (including affected builder/plugins).
- Hardening checklist applied and documented for continuous operations.
Chain of Custody
- Initial preservation: collection without destructive cleanup before forensic inventory.
- Evidence segregation: textual artifacts, binaries, and logs separated by type and origin.
- Change control: remediation only after technical IOC record and decision trail.
- Traceability: commands, outputs, and actions linked to incident timeline.
- Technical delivery: final dossier consolidated for audit, continuity, and future review.
Visual Evidence from the Case
Sanitized evidence record for technical presentation of the engagement (real case images, no exposed personal data):
Initial detection dashboard and incident status.
Evidence of abuse in content/posts.
Triage of suspicious artifacts during sanitation.
Remediation execution and security adjustments.
Final post-hardening validation.
Prioritized Lessons (Hardening Backlog)
- P1 - Plugin governance: remove components without active maintenance and enforce a formal patch window.
- P1 - Privilege control: periodic admin review, MFA, and least-privilege principle.
- P1 - Detection: continuous monitoring for privileged user creation and mass content changes.
- P2 - Integrity baseline: snapshots/versioning of critical files for fast post-incident diff.
- P2 - IR playbook: standardized containment/forensics/remediation runbook to reduce MTTR.
Delivery Standard
Structured delivery in real incident format: containment, investigation, eradication, recovery, and hardening. This is the same model used in day-to-day operations for high-risk Linux/WordPress environments, focused on technical evidence and safe production recovery.
Discuss this service
Do you want to apply this incident response model in your environment with evidence-driven technical execution?