image_01 - Technical case overview.
Executive Summary
Technical WordPress incident engagement for anonymized client (inte***), with application compromise, mass malicious content creation, and persistence through webshell files. The engagement followed a four-phase incident response methodology: containment, forensics, eradication, and hardening.
Technical lead: Percio Andrade Castelo Branco (Infrastructure and Cyber Defense).
Scope and Engagement Assumptions
- Affected platform: WordPress (application layer).
- Host impact: no evidence of structural compromise in base hosting.
- Operational severity: 6/10 (moderate incident with relevant functional compromise).
- Attacker objective: use the site as a malicious content distribution and redirect point.
Identified Attack Chain
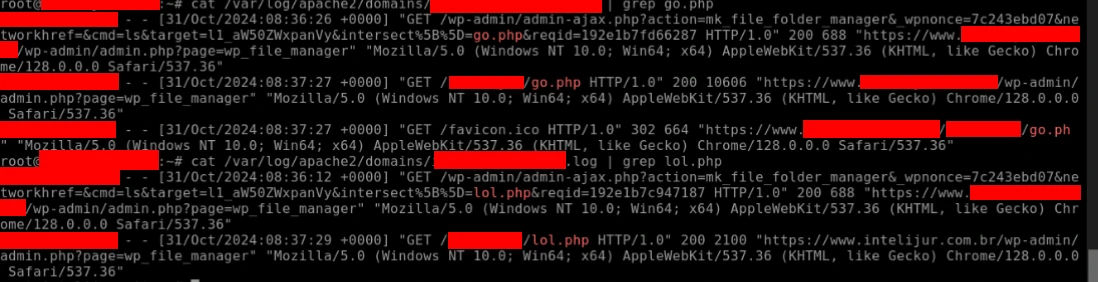
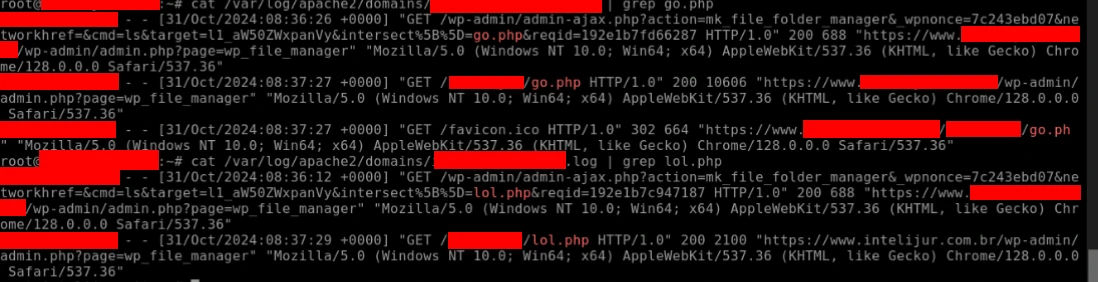
- Massive XML-RPC brute-force attempts (high volume in short time window).
- Administrative WordPress access obtained (hypothesis supported by action traces in admin panel).
- Use of a file manager plugin to upload payloads
go.phpandlol.php. - Deployment of ZIP persistence package (
2022a.zip) containing fallback file. - Active theme switching and template edits (header/footer) to support malicious campaign.
- Automated mass generation of unauthorized content (191 posts).
Confirmed Technical Indicators (IOC)
Artifacts directly linked to the incident, sanitized for publication:
/home/inte***/public_html/inte***/go.php
/home/inte***/public_html/inte***/lol.php
/home/inte***/public_html/wp-content/uploads/2022a.zip
/home/inte***/public_html/wp-content/uploads/2022a.zip/a.php
/home/inte***/wp-content/mu-plugins/index.php
/home/inte***/wp-content/mu-plugins/2022a.zip- Behavioral IOC: creation of hundreds of unauthorized posts.
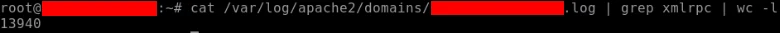
- Authentication IOC: 13,940 XML-RPC brute-force attempts recorded.
- Integrity IOC: unauthorized active theme change and visual template modifications.
Operational Timeline (T0/T1/T2...)
- T0 - Activation: incident intake with signs of malicious content and layout defacement.
- T1 - Containment: site removal from original environment and migration to isolated alternative server.
- T2 - Forensics: artifact collection, log analysis (server + WordPress), and vector/IOC validation.
- T3 - Eradication: payload removal, post cleanup, theme/plugin review, and alteration correction.
- T4 - Hardening: stack updates, firewall/app security reinforcement, credential rotation, and additional controls.
- T5 - Validation: final scan, functional validation, and post-incident technical dossier issuance.
Technical Execution by Phase
Phase 1 - Containment
- Immediate environment isolation to stop real-time attacker actions.
- Evidence and baseline preservation before destructive cleanup.
- Preparation of secure remote environment for incident handling.
Phase 2 - Forensics
- Database and application/server log analysis.
- Signature-based detection (hash/known patterns) and heuristics.
- Scanning with auxiliary scripts (Shell/Python) for batch triage.
- Validation with Wordfence (basic/advanced scan) to reinforce coverage.
Phase 3 - Eradication
- Manual removal of
go.php,lol.php, and compressed persistence artifacts. - Cleanup of unauthorized content and rollback of malicious visual changes.
- Active theme rollback to previously identified legitimate baseline.
Phase 4 - Hardening
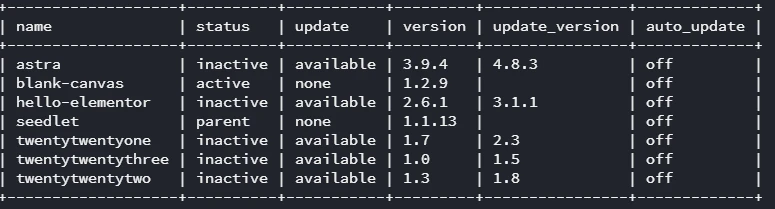
- Update of all plugins, themes, and WordPress core to current versions.
- Wordfence activation with firewall in advanced mode.
- Installation of admin surface hardening plugin (HideMyWP) for later stage in final environment.
- Application of
.htaccesscontrols and XML-RPC disablement/restriction as required. - Full credential rotation for privileged users and database (values suppressed in this public report).
Operational Commands and Routines (Representative)
# 1) Initial inventory of PHP changes
find /var/www/site -type f -name "*.php" -mtime -30 | sort
# 2) Search for common obfuscation/webshell patterns
grep -RniE "base64_decode|gzinflate|eval\\(|assert\\(|preg_replace\\(.*/e" /var/www/site
# 3) Administrative user review
wp user list --role=administrator --path=/var/www/site
# 4) Cache cleanup and environment revalidation
wp cache flush --path=/var/www/site
wp core is-installed --path=/var/www/site
wp plugin list --path=/var/www/site
# 5) Permission reinforcement after remediation
find /var/www/site -type d -exec chmod 755 {} \\\;
find /var/www/site -type f -exec chmod 644 {} \\\;
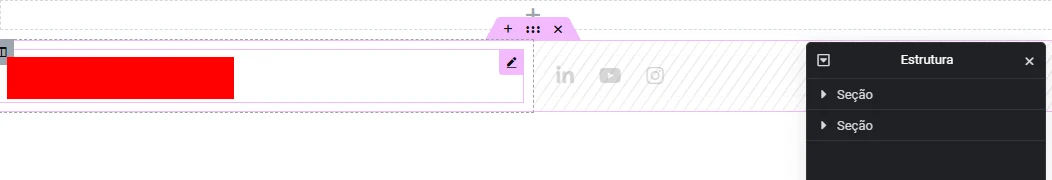
chown -R www-data:www-data /var/www/siteElementor and Layout Integrity
During analysis, it was confirmed that the attacker also edited builder templates (header/footer and structural pages), causing visual and functional frontend impact. Because valid versioning was unavailable for some templates in the compromised environment, reconstruction/correction had to start from technical baseline.
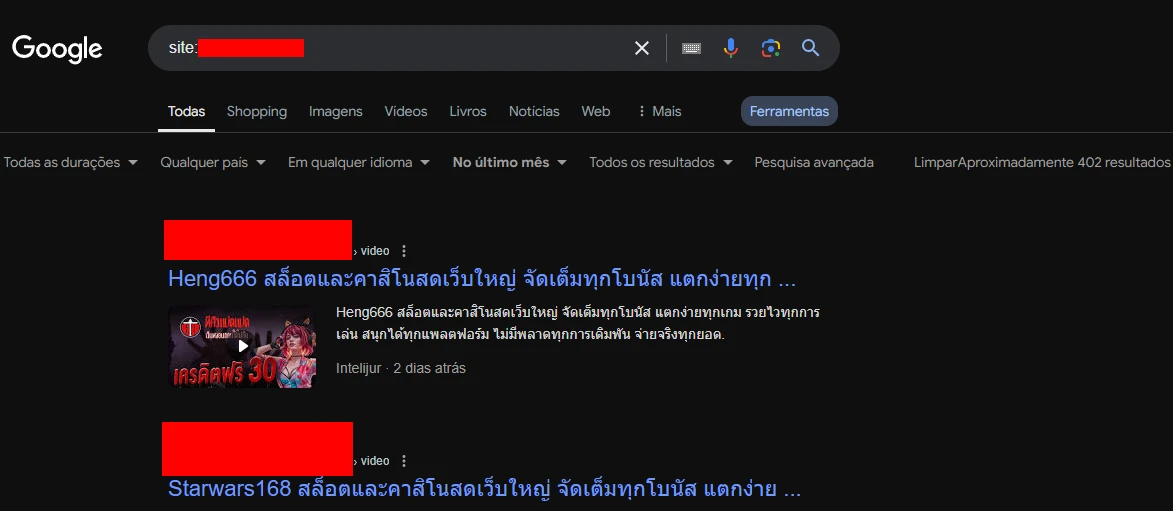
SEO/Reputation Impact
- Unauthorized indexing of attacker-generated pages (402 results observed in analysis period).
- Need for index cleanup, valid sitemap resubmission, and malicious URL pattern removal.
- Recommendation for continuous reputation monitoring to reduce persistence of indexed junk.
Operational Metrics and Outcome
- Environment recovered from compromised state to stable functional operation.
- 191 malicious posts identified and treated in eradication scope.
- 13,940 XML-RPC brute-force attempts confirmed in log trails.
- Administrative surface hardened with additional protection layers.
Visual Evidence from the Engagement
Sanitized technical screenshots (no sensitive data):
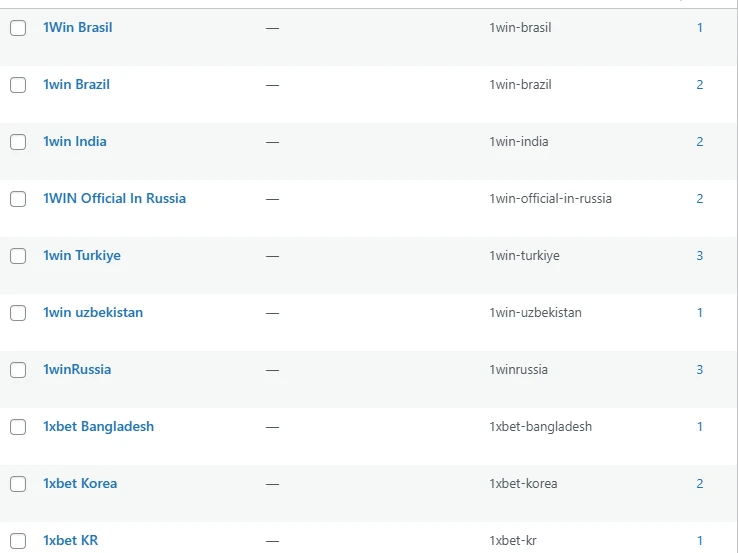
image_02 - Initial artifact linked to the incident.
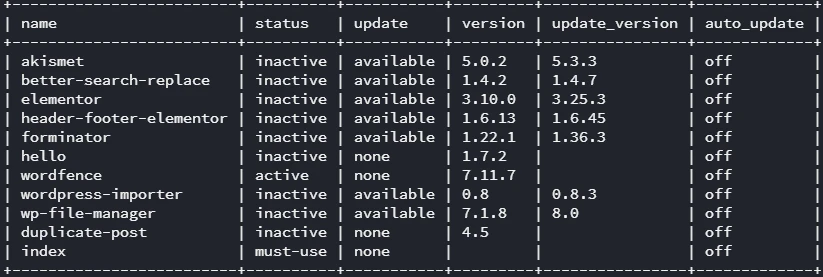
image_03 - Attack trail with payload delivered to the environment.

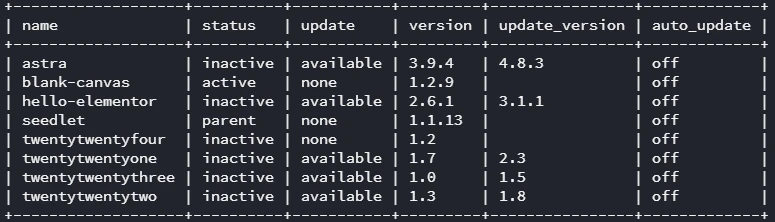
image_04 - Persistence/re-entry point evidence.

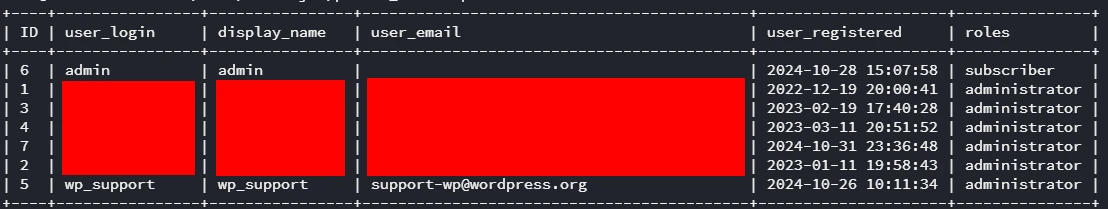
image_05 - Technical validation of incident logs.
image_06 - Mass cleanup of unauthorized content.
image_07 - Hardening stage applied.
image_08 - Reinforcement of security controls.
image_09 - Review/fix of affected templates.
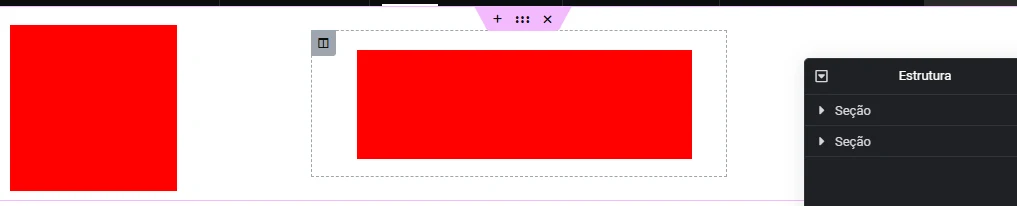
image_10 - Post-remediation state with stable baseline.
image_11 - Final remediation validation.
image_12 - Final proof of technical delivery.
Prioritized Lessons (Security Backlog)
- P1 - Authentication control: robust XML-RPC and administrative authentication protection.
- P1 - Plugin governance: reduce risky plugins and review operational permissions.
- P1 - Monitoring: alert on mass post creation and theme/template changes.
- P2 - Recovery: versioning of critical templates (header/footer/home) for fast rollback.
- P2 - Reputation: indexing sanitization routine and post-incident SEO monitoring.
Document Reference
Based on anonymized technical dossier: INTEL***_SECURITY-2.0.
Discuss this service
Do you want to apply this incident response model in your environment with evidence-driven technical execution?